
How AI-Enabled Workflow Automation Can Help SOCs Reduce Burnout
It sure is a hard time to be a SOC analyst. Every day, they are expected to solve high-consequence problems with half the data and

It sure is a hard time to be a SOC analyst. Every day, they are expected to solve high-consequence problems with half the data and

Google has revealed the various safety measures that are being incorporated into its generative artificial intelligence (AI) systems to mitigate emerging attack vectors like indirect
Not every risk looks like an attack. Some problems start as small glitches, strange logs, or quiet delays that don’t seem urgent—until they are. What
The April 2025 cyber attacks targeting U.K. retailers Marks & Spencer and Co-op have been classified as a “single combined cyber event.” That’s according to
The threat actors behind the Qilin ransomware-as-a-service (RaaS) scheme are now offering legal counsel for affiliates to put more pressure on victims to pay up,

Iran’s state-owned TV broadcaster was hacked Wednesday night to interrupt regular programming and air videos calling for street protests against the Iranian government, according to
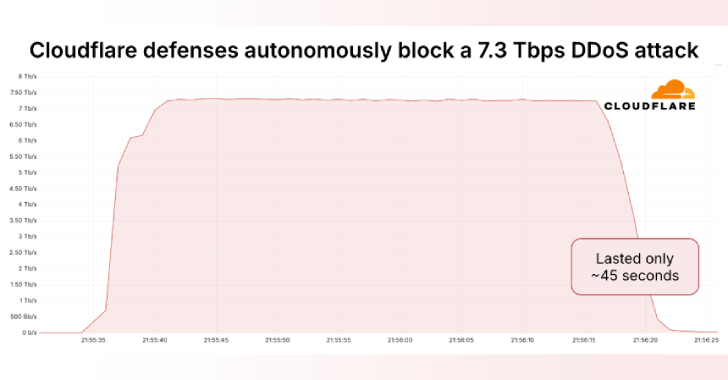
Cloudflare on Thursday said it autonomously blocked the largest ever distributed denial-of-service (DDoS) attack ever recorded, which hit a peak of 7.3 terabits per second

Hackers never sleep, so why should enterprise defenses? Threat actors prefer to target businesses during off-hours. That’s when they can count on fewer security personnel

Cybersecurity researchers have uncovered a new campaign in which the threat actors have published more than 67 GitHub repositories that claim to offer Python-based hacking
Cybersecurity researchers have exposed the inner workings of an Android malware called AntiDot that has compromised over 3,775 devices as part of 273 unique campaigns.
