
How Top CISOs Save Their SOCs from Alert Chaos to Never Miss Real Incidents
Why do SOC teams still drown in alerts even after spending big on security tools? False positives pile up, stealthy threats slip through, and critical

Why do SOC teams still drown in alerts even after spending big on security tools? False positives pile up, stealthy threats slip through, and critical

Cybersecurity researchers have lifted the veil on a widespread malicious campaign that’s targeting TikTok Shop users globally with an aim to steal credentials and distribute

SonicWall said it’s actively investigating reports to determine if there is a new zero-day vulnerability following reports of a spike in Akira ransomware actors in
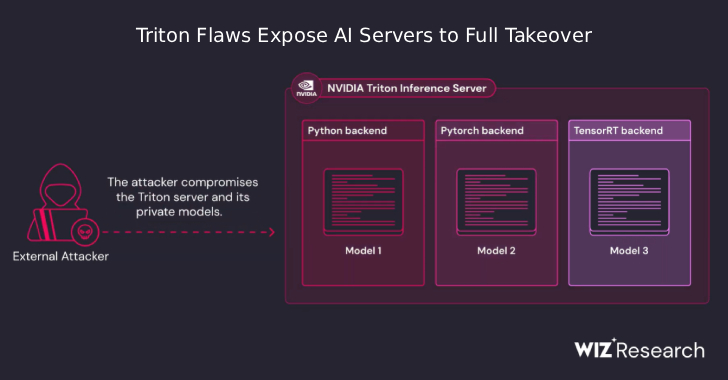
A newly disclosed set of security flaws in NVIDIA’s Triton Inference Server for Windows and Linux, an open-source platform for running artificial intelligence (AI) models
Cybersecurity researchers are calling attention to a new wave of campaigns distributing a Python-based information stealer called PXA Stealer. The malicious activity has been assessed

Some of the most devastating cyberattacks don’t rely on brute force, but instead succeed through stealth. These quiet intrusions often go unnoticed until long after

Malware isn’t just trying to hide anymore—it’s trying to belong. We’re seeing code that talks like us, logs like us, even documents itself like a
Everyone’s an IT decision-maker now. The employees in your organization can install a plugin with just one click, and they don’t need to clear it

Cybersecurity researchers have discovered a nascent Android remote access trojan (RAT) called PlayPraetor that has infected more than 11,000 devices, primarily across Portugal, Spain, France,

Telecommunications organizations in Southeast Asia have been targeted by a state-sponsored threat actor known as CL-STA-0969 to facilitate remote control over compromised networks. Palo Alto
