
Apple Patches CVE-2025-43300 Zero-Day in iOS, iPadOS, and macOS Exploited in Targeted Attacks
Apple has released security updates to address a security flaw impacting iOS, iPadOS, and macOS that it said has come under active exploitation in the

Apple has released security updates to address a security flaw impacting iOS, iPadOS, and macOS that it said has come under active exploitation in the

A Russian state-sponsored cyber espionage group known as Static Tundra has been observed actively exploiting a seven-year-old security flaw in Cisco IOS and Cisco IOS
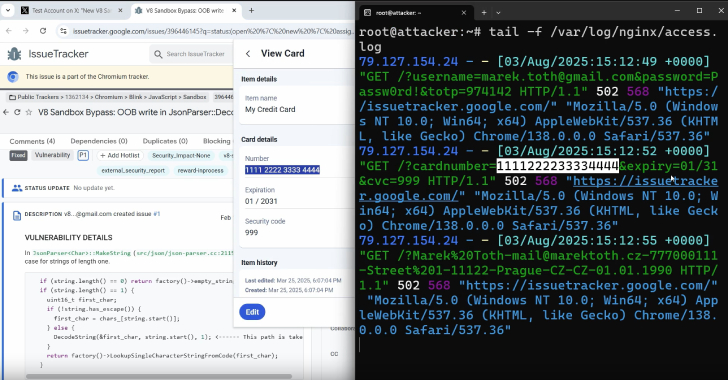
Popular password manager plugins for web browsers have been found susceptible to clickjacking security vulnerabilities that could be exploited to steal account credentials, two-factor authentication
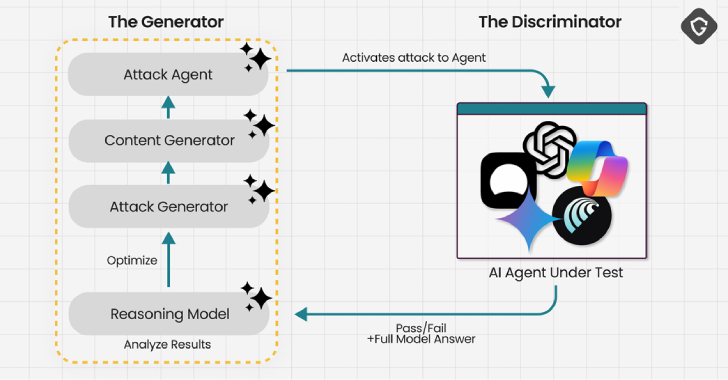
Cybersecurity researchers have demonstrated a new prompt injection technique called PromptFix that tricks a generative artificial intelligence (GenAI) model into carrying out intended actions by

Do you know how many AI agents are running inside your business right now? If the answer is “not sure,” you’re not alone—and that’s exactly

Modern businesses face a rapidly evolving and expanding threat landscape, but what does this mean for your business? It means a growing number of risks,

North Korean threat actors have been attributed to a coordinated cyber espionage campaign targeting diplomatic missions in their southern counterpart between March and July 2025.

A 22-year-old man from the U.S. state of Oregon has been charged with allegedly developing and overseeing a distributed denial-of-service (DDoS)-for-hire botnet called RapperBot. Ethan
Threat actors are exploiting a nearly two-year-old security flaw in Apache ActiveMQ to gain persistent access to cloud Linux systems and deploy malware called DripDropper.

Financial institutions like trading and brokerage firms are the target of a new campaign that delivers a previously unreported remote access trojan called GodRAT. The
