
The 5 Golden Rules of Safe AI Adoption
Employees are experimenting with AI at record speed. They are drafting emails, analyzing data, and transforming the workplace. The problem is not the pace of

Employees are experimenting with AI at record speed. They are drafting emails, analyzing data, and transforming the workplace. The problem is not the pace of
Cybersecurity researchers have discovered five distinct activity clusters linked to a persistent threat actor known as Blind Eagle between May 2024 and July 2025. These

A widespread data theft campaign has allowed hackers to breach sales automation platform Salesloft to steal OAuth and refresh tokens associated with the Drift artificial
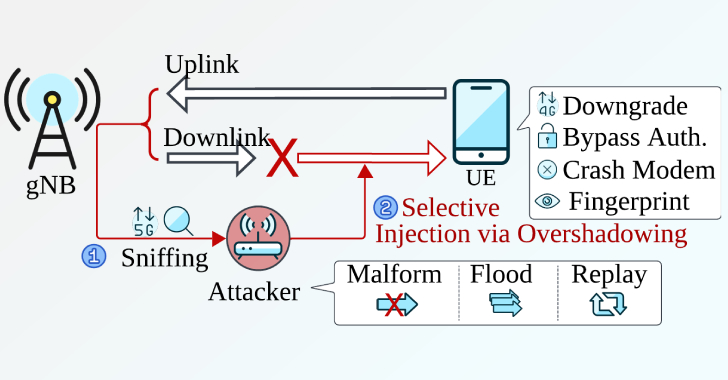
A team of academics has devised a novel attack that can be used to downgrade a 5G connection to a lower generation without relying on

Citrix has released fixes to address three security flaws in NetScaler ADC and NetScaler Gateway, including one that it said has been actively exploited in

Cybersecurity researchers are calling attention to a sophisticated social engineering campaign that’s targeting supply chain-critical manufacturing companies with an in-memory malware dubbed MixShell. The activity

A new large-scale campaign has been observed exploiting over 100 compromised WordPress sites to direct site visitors to fake CAPTCHA verification pages that employ the

Cybersecurity researchers have discovered a new variant of an Android banking trojan called HOOK that features ransomware-style overlay screens to display extortion messages. “A prominent

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added three security flaws impacting Citrix Session Recording and Git to its Known Exploited Vulnerabilities
Google has announced plans to begin verifying the identity of all developers who distribute apps on Android, even for those who distribute their software outside
