
Automation Is Redefining Pentest Delivery
Pentesting remains one of the most effective ways to identify real-world security weaknesses before adversaries do. But as the threat landscape has evolved, the way

Pentesting remains one of the most effective ways to identify real-world security weaknesses before adversaries do. But as the threat landscape has evolved, the way
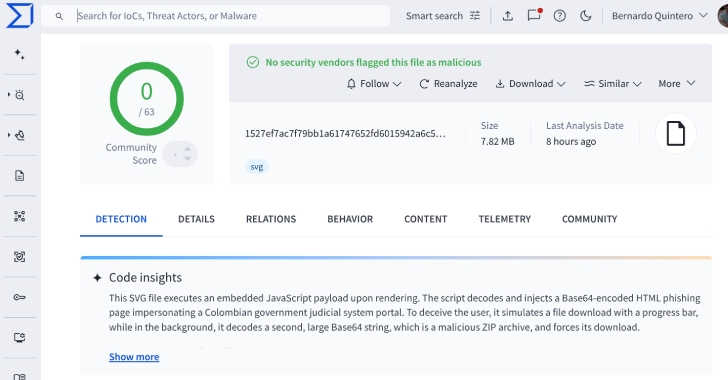
Cybersecurity researchers have flagged a new malware campaign that has leveraged Scalable Vector Graphics (SVG) files as part of phishing attacks impersonating the Colombian judicial

Cybersecurity researchers have lifted the lid on a previously undocumented threat cluster dubbed GhostRedirector that has managed to compromise at least 65 Windows servers primarily

The Russian state-sponsored hacking group tracked as APT28 has been attributed to a new Microsoft Outlook backdoor called NotDoor in attacks targeting multiple companies from

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added two security flaws impacting TP-Link wireless routers to its Known Exploited Vulnerabilities (KEV) catalog,

The French data protection authority has fined Google and Chinese e-commerce giant Shein $379 million (€325 million) and $175 million (€150 million), respectively, for violating

Cybersecurity researchers have flagged a new technique that cybercriminals have adopted to bypass social media platform X’s malvertising protections and propagate malicious links using its

Cybersecurity researchers have discovered two new malicious packages on the npm registry that make use of smart contracts for the Ethereum blockchain to carry out

Google has shipped security updates to address 120 security flaws in its Android operating system as part of its monthly fixes for September 2025, including

In January 2025, cybersecurity experts at Wiz Research found that Chinese AI specialist DeepSeek had suffered a data leak, putting more than 1 million sensitive
