
Learn How Leading Companies Secure Cloud Workloads and Infrastructure at Scale
You’ve probably already moved some of your business to the cloud—or you’re planning to. That’s a smart move. It helps you work faster, serve your

You’ve probably already moved some of your business to the cloud—or you’re planning to. That’s a smart move. It helps you work faster, serve your
Microsoft on Monday disclosed that it automatically detected and neutralized a distributed denial-of-service (DDoS) attack targeting a single endpoint in Australia that measured 5.72 terabits

Google on Monday released security updates for its Chrome browser to address two security flaws, including one that has come under active exploitation in the
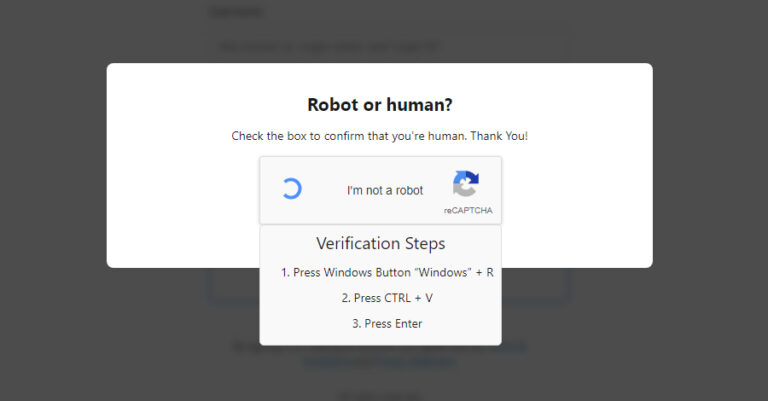
Cybersecurity researchers have discovered malware campaigns using the now-prevalent ClickFix social engineering tactic to deploy Amatera Stealer and NetSupport RAT. The activity, observed this month,

Phishing attacks are no longer confined to the email inbox, with 1 in 3 phishing attacks now taking place over non-email channels like social media,

This week showed just how fast things can go wrong when no one’s watching. Some attacks were silent and sneaky. Others used tools we trust
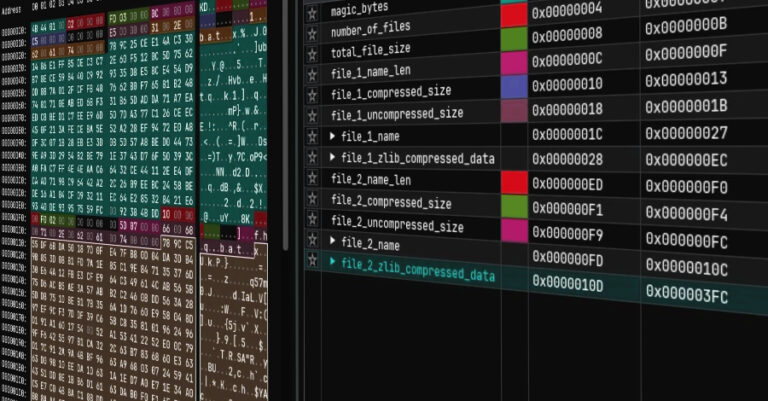
The threat actor known as Dragon Breath has been observed making use of a multi-stage loader codenamed RONINGLOADER to deliver a modified variant of a

Google has disclosed that the company’s continued adoption of the Rust programming language in Android has resulted in the number of memory safety vulnerabilities falling

The botnet malware known as RondoDox has been observed targeting unpatched XWiki instances against a critical security flaw that could allow attackers to achieve arbitrary

The U.S. Department of Justice (DoJ) on Friday announced that five individuals have pleaded guilty to assisting North Korea’s illicit revenue generation schemes by enabling
