
Unpatched PHP Voyager Flaws Leave Servers Open to One-Click RCE Exploits
Three security flaws have been disclosed in the open-source PHP package Voyager that could be exploited by an attacker to achieve one-click remote code execution

Three security flaws have been disclosed in the open-source PHP package Voyager that could be exploited by an attacker to achieve one-click remote code execution

The North Korean threat actor known as the Lazarus Group has been observed leveraging a “web-based administrative platform” to oversee its command-and-control (C2) infrastructure, giving
A team of security researchers from Georgia Institute of Technology and Ruhr University Bochum has demonstrated two new side-channel attacks targeting Apple silicon that could

Curious about the buzz around AI in cybersecurity? Wonder if it’s just a shiny new toy in the tech world or a serious game changer?
A critical security flaw has been disclosed in the Cacti open-source network monitoring and fault management framework that could allow an authenticated attacker to achieve

Ransomware attacks have reached an unprecedented scale in the healthcare sector, exposing vulnerabilities that put millions at risk. Recently, UnitedHealth revealed that 190 million Americans
Broadcom has alerted of a high-severity security flaw in VMware Avi Load Balancer that could be weaponized by malicious actors to gain entrenched database access.

Cybersecurity researchers are warning that a critical zero-day vulnerability impacting Zyxel CPE Series devices is seeing active exploitation attempts in the wild. “Attackers can leverage

The advanced persistent threat (APT) group known as UAC-0063 has been observed leveraging legitimate documents obtained by infiltrating one victim to attack another target with
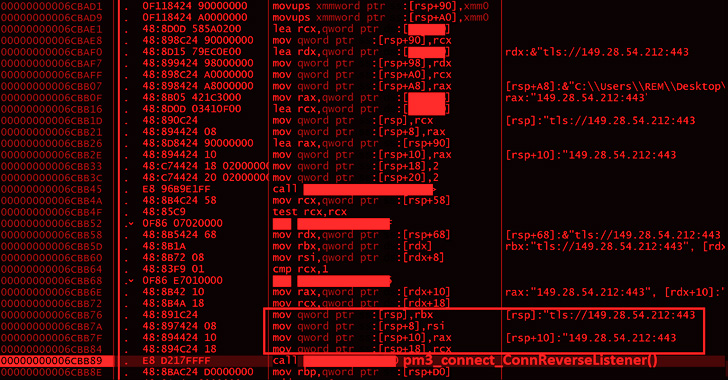
A financially motivated threat actor has been linked to an ongoing phishing email campaign that has been ongoing since at least July 2024 specifically targeting
