
The Hidden Weaknesses in AI SOC Tools that No One Talks About
If you’re evaluating AI-powered SOC platforms, you’ve likely seen bold claims: faster triage, smarter remediation, and less noise. But under the hood, not all AI

If you’re evaluating AI-powered SOC platforms, you’ve likely seen bold claims: faster triage, smarter remediation, and less noise. But under the hood, not all AI

Cisco has released security updates to address a maximum-severity security flaw in Unified Communications Manager (Unified CM) and Unified Communications Manager Session Management Edition (Unified

Threat actors with ties to North Korea have been observed targeting Web3 and cryptocurrency-related businesses with malware written in the Nim programming language, underscoring a

With nearly 80% of cyber threats now mimicking legitimate user behavior, how are top SOCs determining what’s legitimate traffic and what is potentially dangerous? Where

Cybersecurity researchers are calling attention to phishing campaigns that impersonate popular brands and trick targets into calling phone numbers operated by threat actors. “A significant

The U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC) has levied sanctions against Russia-based bulletproof hosting (BPH) service provider Aeza Group to
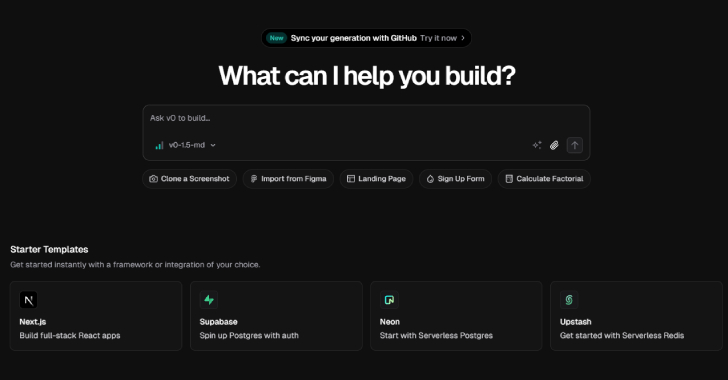
Unknown threat actors have been observed weaponizing v0, a generative artificial intelligence (AI) tool from Vercel, to design fake sign-in pages that impersonate their legitimate
Cybersecurity researchers have discovered a critical security vulnerability in artificial intelligence (AI) company Anthropic’s Model Context Protocol (MCP) Inspector project that could result in remote

Cybersecurity researchers have flagged the tactical similarities between the threat actors behind the RomCom RAT and a cluster that has been observed delivering a loader
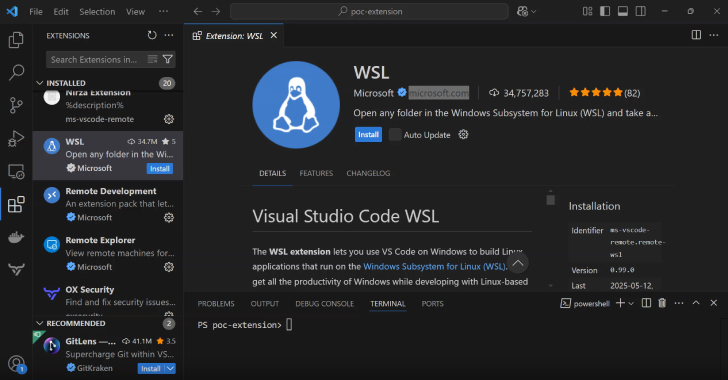
A new study of integrated development environments (IDEs) like Microsoft Visual Studio Code, Visual Studio, IntelliJ IDEA, and Cursor has revealed weaknesses in how they
