New Win-DDoS Flaws Let Attackers Turn Public Domain Controllers into DDoS Botnet via RPC, LDAP
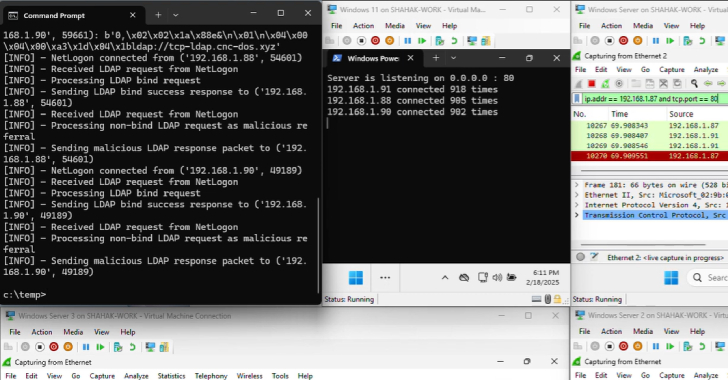
A novel attack technique could be weaponized to rope thousands of public domain controllers (DCs) around the world to create a malicious botnet and use
A novel attack technique could be weaponized to rope thousands of public domain controllers (DCs) around the world to create a malicious botnet and use
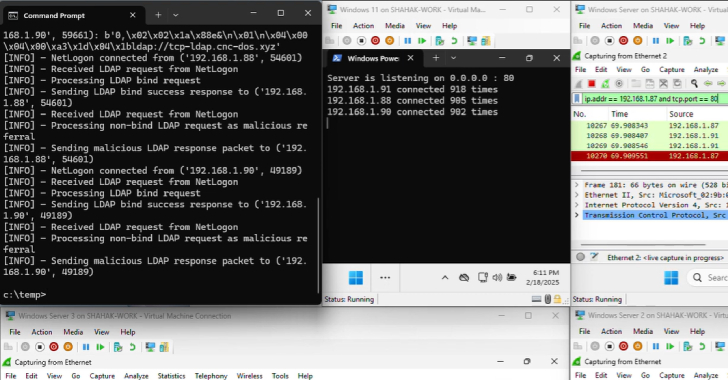
Cybersecurity researchers have presented new findings related to a now-patched security issue in Microsoft’s Windows Remote Procedure Call (RPC) communication protocol that could be abused
Cybersecurity researchers have uncovered multiple security flaws in Dell’s ControlVault3 firmware and its associated Windows APIs that could have been abused by attackers to bypass

Cybersecurity researchers have disclosed vulnerabilities in select model webcams from Lenovo that could turn them into BadUSB attack devices. “This allows remote attackers to inject

Cybersecurity researchers have uncovered a jailbreak technique to bypass ethical guardrails erected by OpenAI in its latest large language model (LLM) GPT-5 and produce illicit

Cybersecurity researchers have discovered over a dozen vulnerabilities in enterprise secure vaults from CyberArk and HashiCorp that, if successfully exploited, can allow remote attackers to

Cybersecurity researchers are drawing attention to a new campaign that’s using legitimate generative artificial intelligence (AI)-powered website building tools like DeepSite AI and BlackBox AI

When an organization’s credentials are leaked, the immediate consequences are rarely visible—but the long-term impact is far-reaching. Far from the cloak-and-dagger tactics seen in fiction,
A fresh set of 60 malicious packages has been uncovered targeting the RubyGems ecosystem by posing as seemingly innocuous automation tools for social media, blogging,

A newly discovered campaign dubbed GreedyBear has leveraged over 150 malicious extensions to the Firefox marketplace that are designed to impersonate popular cryptocurrency wallets and
