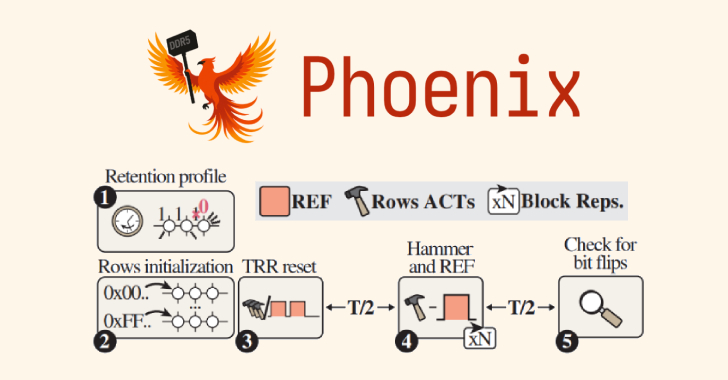
Phoenix RowHammer Attack Bypasses Advanced DDR5 Memory Protections in 109 Seconds
A team of academics from ETH Zürich and Google has discovered a new variant of a RowHammer attack targeting Double Data Rate 5 (DDR5) memory
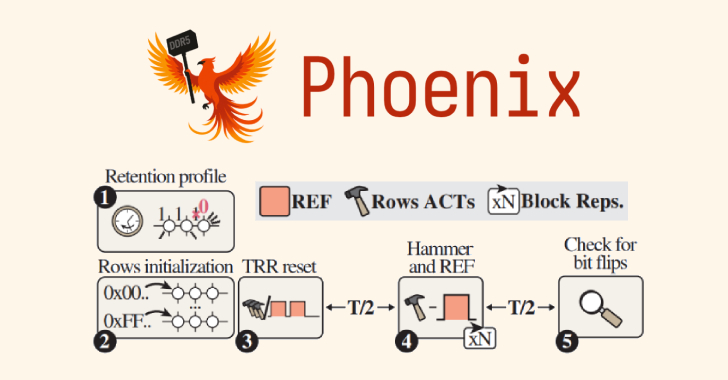
A team of academics from ETH Zürich and Google has discovered a new variant of a RowHammer attack targeting Double Data Rate 5 (DDR5) memory

Cybersecurity researchers have flagged a fresh software supply chain attack targeting the npm registry that has affected more than 40 packages that belong to multiple

The China-aligned threat actor known as Mustang Panda has been observed using an updated version of a backdoor called TONESHELL and a previously undocumented USB
Attacks that target users in their web browsers have seen an unprecedented rise in recent years. In this article, we’ll explore what a “browser-based attack”

In a world where threats are persistent, the modern CISO’s real job isn’t just to secure technology—it’s to preserve institutional trust and ensure business continuity.

A new artificial intelligence (AI)-powered penetration testing tool linked to a China-based company has attracted nearly 11,000 downloads on the Python Package Index (PyPI) repository,

Chinese-speaking users are the target of a search engine optimization (SEO) poisoning campaign that uses fake software sites to distribute malware. “The attackers manipulated search

The U.S. Federal Bureau of Investigation (FBI) has issued a flash alert to release indicators of compromise (IoCs) associated with two cybercriminal groups tracked as
Samsung has released its monthly security updates for Android, including a fix for a security vulnerability that it said has been exploited in zero-day attacks.

Apple has notified users in France of a spyware campaign targeting their devices, according to the Computer Emergency Response Team of France (CERT-FR). The agency
