
Confucius Hackers Hit Pakistan With New WooperStealer and Anondoor Malware
The threat actor known as Confucius has been attributed to a new phishing campaign that has targeted Pakistan with malware families like WooperStealer and Anondoor.

The threat actor known as Confucius has been attributed to a new phishing campaign that has targeted Pakistan with malware families like WooperStealer and Anondoor.

Cybersecurity researchers have flagged a malicious package on the Python Package Index (PyPI) repository that claims to offer the ability to create a SOCKS5 proxy

Google Mandiant and Google Threat Intelligence Group (GTIG) have disclosed that they are tracking a new cluster of activity possibly linked to a financially motivated

Penetration testing is critical to uncovering real-world security weaknesses. With the shift into continuous testing and validation, it is time we automate the delivery of

From unpatched cars to hijacked clouds, this week’s Threatsday headlines remind us of one thing — no corner of technology is safe. Attackers are scanning
Running a SOC often feels like drowning in alerts. Every morning, dashboards light up with thousands of signals; some urgent, many irrelevant. The job is
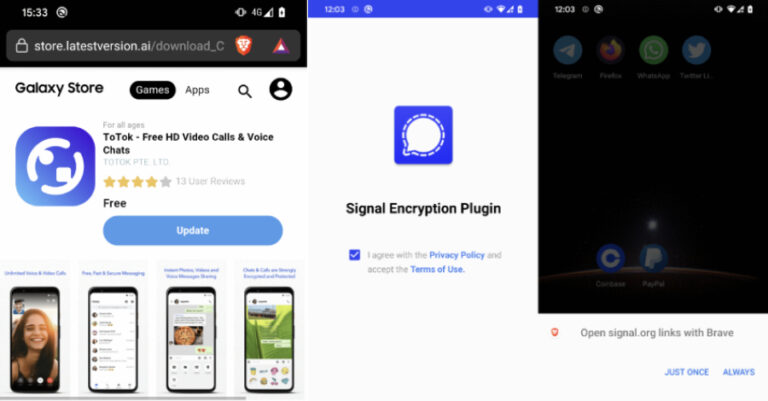
Cybersecurity researchers have discovered two Android spyware campaigns dubbed ProSpy and ToSpy that impersonate apps like Signal and ToTok to target users in the United
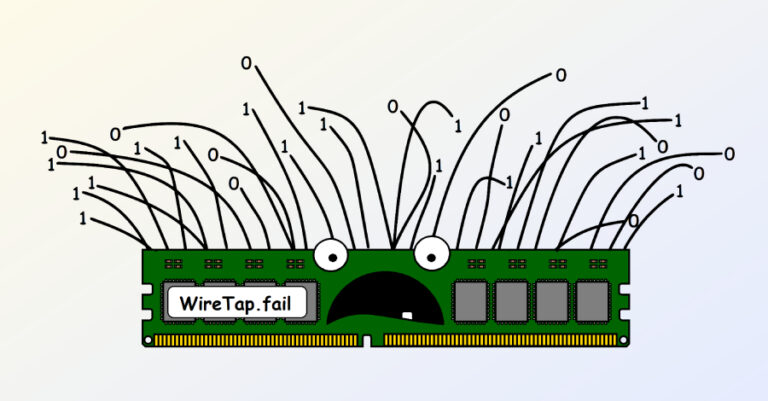
In yet another piece of research, academics from Georgia Institute of Technology and Purdue University have demonstrated that the security guarantees offered by Intel’s Software
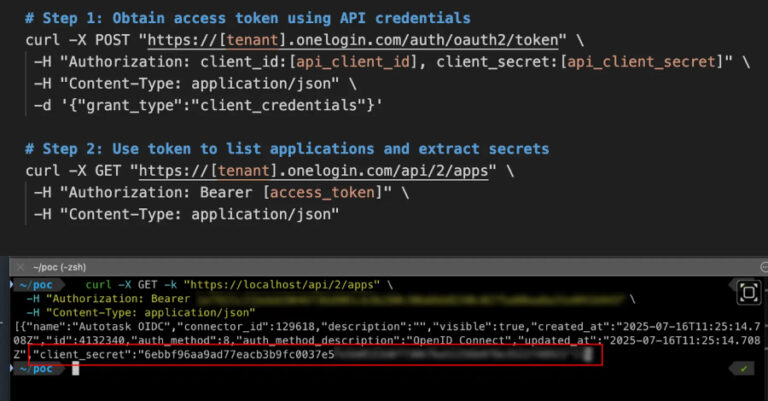
A high-severity security flaw has been disclosed in the One Identity OneLogin Identity and Access Management (IAM) solution that, if successfully exploited, could expose sensitive
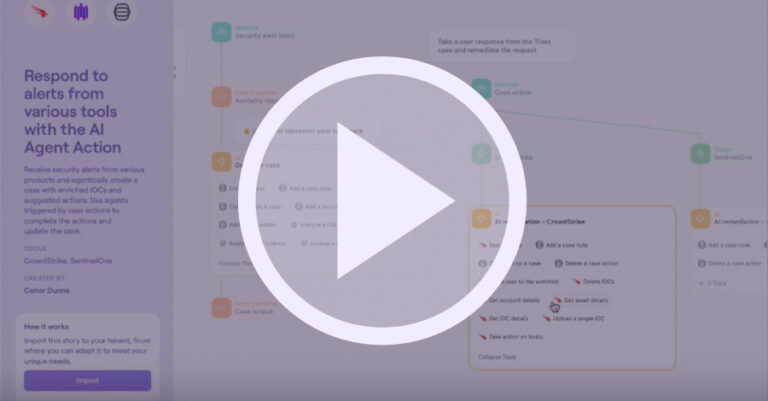
AI is changing automation—but not always for the better. That’s why we’re hosting a new webinar, “Workflow Clarity: Where AI Fits in Modern Automation,” with
