The Death of the Security Checkbox: BAS Is the Power Behind Real Defense
Security doesn’t fail at the point of breach. It fails at the point of impact. That line set the tone for this year’s Picus Breach
Security doesn’t fail at the point of breach. It fails at the point of impact. That line set the tone for this year’s Picus Breach
Cybersecurity researchers have uncovered yet another active software supply chain attack campaign targeting the npm registry with over 100 malicious packages that can steal authentication
The comfort zone in cybersecurity is gone. Attackers are scaling down, focusing tighter, and squeezing more value from fewer, high-impact targets. At the same time,

Cybersecurity researchers have flagged a new security issue in agentic web browsers like OpenAI ChatGPT Atlas that exposes underlying artificial intelligence (AI) models to context
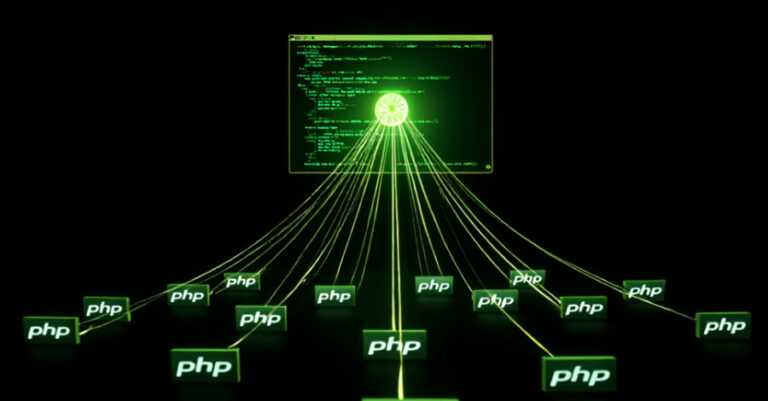
Cybersecurity researchers are calling attention to a spike in automated attacks targeting PHP servers, IoT devices, and cloud gateways by various botnets such as Mirai,

Organizations in Ukraine have been targeted by threat actors of Russian origin with an aim to siphon sensitive data and maintain persistent access to compromised

BeyondTrust’s annual cybersecurity predictions point to a year where old defenses will fail quietly, and new attack vectors will surge. Introduction The next major breach

Artificial Intelligence (AI) is rapidly transforming Governance, Risk, and Compliance (GRC). It’s no longer a future concept—it’s here, and it’s already reshaping how teams operate.

Cybersecurity researchers have discovered a set of 10 malicious npm packages that are designed to deliver an information stealer targeting Windows, Linux, and macOS systems.

Threat actors are actively exploiting multiple security flaws impacting Dassault Systèmes DELMIA Apriso and XWiki, according to alerts issued by the U.S. Cybersecurity and Infrastructure
