
APT28 Uses BEARDSHELL and COVENANT Malware to Spy on Ukrainian Military
The Russian state-sponsored hacking group tracked as APT28 has been observed using a pair of implants dubbed BEARDSHELL and COVENANT to facilitate long‑term surveillance of

The Russian state-sponsored hacking group tracked as APT28 has been observed using a pair of implants dubbed BEARDSHELL and COVENANT to facilitate long‑term surveillance of
You can’t control when the next critical vulnerability drops. You can control how much of your environment is exposed when it does. The problem is

Artificial Intelligence (AI) is no longer just a tool we talk to; it is a tool that does things for us. These are called AI
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added three security flaws to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of

Salesforce has warned of an increase in threat actor activity that’s aimed at exploiting misconfigurations in publicly accessible Experience Cloud sites by making use of
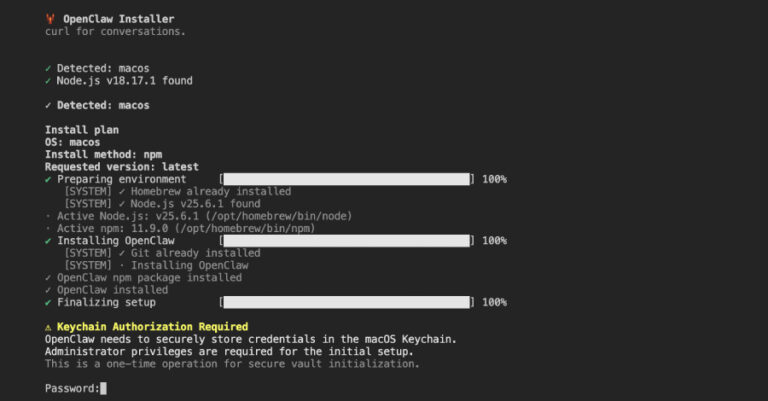
Cybersecurity researchers have discovered a malicious npm package that masquerades as an OpenClaw installer to deploy a remote access trojan (RAT) and steal sensitive data
Another week in cybersecurity. Another week of “you’ve got to be kidding me.” Attackers were busy. Defenders were busy. And somewhere in the middle, a

The North Korean threat actor known as UNC4899 is suspected to be behind a sophisticated cloud compromise campaign targeting a cryptocurrency organization in 2025 to

Mid-market organizations are constantly striving to achieve security levels on a par with their enterprise peers. With heightened awareness of supply chain attacks, your customers

Two Google Chrome extensions have turned malicious after what appears to be a case of ownership transfer, offering attackers a way to push malware to
