AI is Everywhere, But CISOs are Still Securing It with Yesterday’s Skills and Tools, Study Finds
A majority of security leaders are struggling to defend AI systems with tools and skills that are not fit for the challenge, according to the
A majority of security leaders are struggling to defend AI systems with tools and skills that are not fit for the challenge, according to the
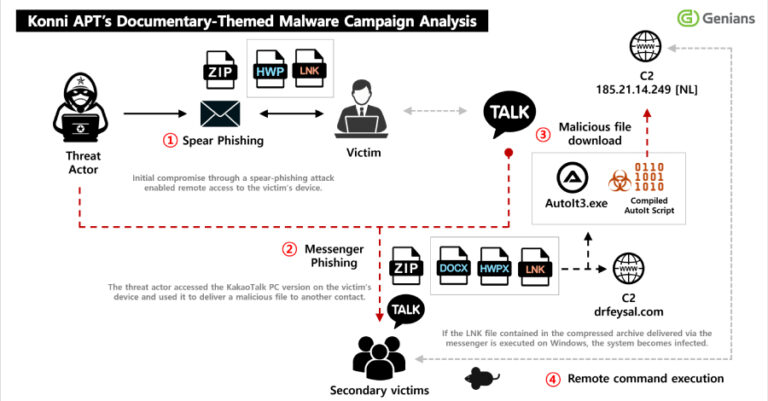
North Korean threat actors have been observed sending phishing to compromise targets and obtain access to a victim’s KakaoTalk desktop application to distribute malicious payloads

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a medium-severity security flaw impacting Wing FTP to its Known Exploited Vulnerabilities (KEV) catalog,
The GlassWorm malware campaign is being used to fuel an ongoing attack that leverages the stolen GitHub tokens to inject malware into hundreds of Python
Some weeks in security feel normal. Then you read a few tabs and get that immediate “ah, great, we’re doing this now” feeling. This week

If you run security at any reasonably complex organization, your validation stack probably looks something like this: a BAS tool in one corner. A pentest

Three different ClickFix campaigns have been found to act as a delivery vector for the deployment of a macOS information stealer called MacSync. “Unlike traditional

Ukrainian entities have emerged as the target of a new campaign likely orchestrated by threat actors linked to Russia, according to a report from S2

Google is testing a new security feature as part of Android Advanced Protection Mode (AAPM) that prevents certain kinds of apps from using the accessibility

China’s National Computer Network Emergency Response Technical Team (CNCERT) has issued a warning about the security stemming from the use of OpenClaw (formerly Clawdbot and
