
Researchers Find Exploit Allowing NTLMv1 Despite Active Directory Restrictions
Cybersecurity researchers have found that the Microsoft Active Directory Group Policy that’s designed to disable NT LAN Manager (NTLM) v1 can be trivially bypassed by

Cybersecurity researchers have found that the Microsoft Active Directory Group Policy that’s designed to disable NT LAN Manager (NTLM) v1 can be trivially bypassed by

You can tell the story of the current state of stolen credential-based attacks in three numbers: Stolen credentials were the #1 attacker action in 2023/24,

Ivanti has rolled out security updates to address several security flaws impacting Avalanche, Application Control Engine, and Endpoint Manager (EPM), including four critical bugs that

Cybersecurity researchers have detailed an attack that involved a threat actor utilizing a Python-based backdoor to maintain persistent access to compromised endpoints and then leveraged
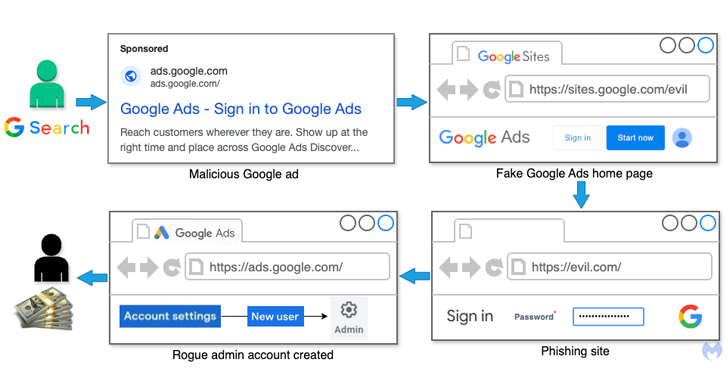
Cybersecurity researchers have alerted to a new malvertising campaign that’s targeting individuals and businesses advertising via Google Ads by attempting to phish for their credentials

The North Korea-linked Lazarus Group has been attributed to a new cyber attack campaign dubbed Operation 99 that targeted software developers looking for freelance Web3

Cybersecurity researchers have identified infrastructure links between the North Korean threat actors behind the fraudulent IT worker schemes and a 2016 crowdfunding scam. The new

As many as six security vulnerabilities have been disclosed in the popular Rsync file-synchronizing tool for Unix systems, some of which could be exploited to

Why does ICS/OT need specific controls and its own cybersecurity budget today? Because treating ICS/OT security with an IT security playbook isn’t just ineffective—it’s high

The U.S. Department of Justice (DoJ) on Tuesday disclosed that a court-authorized operation allowed the Federal Bureau of Investigation (FBI) to delete PlugX malware from
