
⚡ THN Weekly Recap: Top Cybersecurity Threats, Tools and Tips [27 January]
Welcome to your weekly cybersecurity scoop! Ever thought about how the same AI meant to protect our hospitals could also compromise them? This week, we’re

Welcome to your weekly cybersecurity scoop! Ever thought about how the same AI meant to protect our hospitals could also compromise them? This week, we’re

The Open Web Application Security Project has recently introduced a new Top 10 project – the Non-Human Identity (NHI) Top 10. For years, OWASP has

A previously unknown threat actor has been observed copying the tradecraft associated with the Kremlin-aligned Gamaredon hacking group in its cyber attacks targeting Russian-speaking entities.

Threat hunters have detailed an ongoing campaign that leverages a malware loader called MintsLoader to distribute secondary payloads such as the StealC information stealer and
A high-severity security flaw has been disclosed in Meta’s Llama large language model (LLM) framework that, if successfully exploited, could allow an attacker to execute
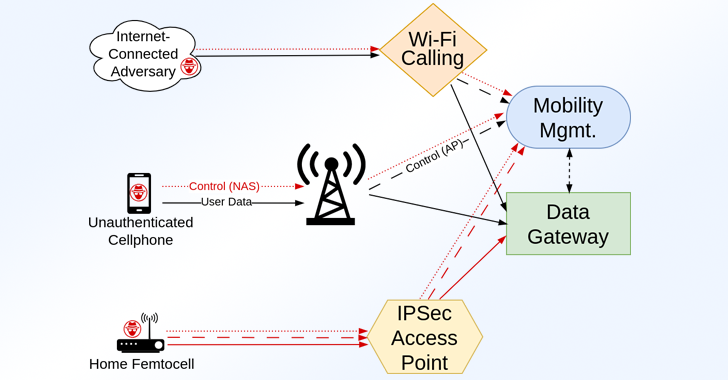
A group of academics has disclosed details of over 100 security vulnerabilities impacting LTE and 5G implementations that could be exploited by an attacker to

The modern workplace has undergone a seismic transformation over recent years, with hybrid work becoming the norm and businesses rapidly adopting cloud-based Software-as-a-Service (SaaS) applications

The U.S. Department of Justice (DoJ) on Thursday indicted two North Korean nationals, a Mexican national, and two of its own citizens for their alleged
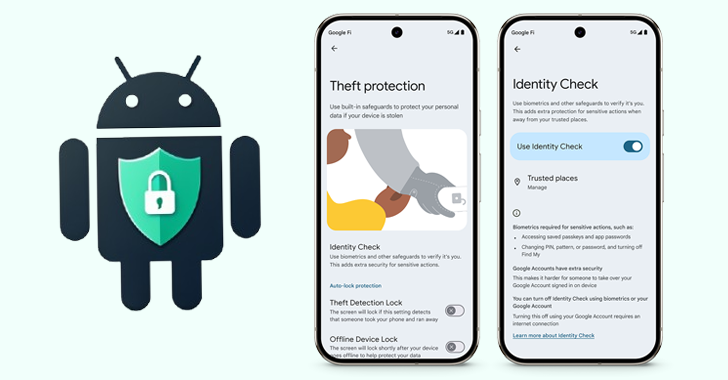
Google has launched a new feature called Identity Check for supported Android devices that locks sensitive settings behind biometric authentication when outside of trusted locations.

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday placed a now-patched security flaw impacting the popular jQuery JavaScript library to its Known Exploited
