Axios Abuse and Salty 2FA Kits Fuel Advanced Microsoft 365 Phishing Attacks
Threat actors are abusing HTTP client tools like Axios in conjunction with Microsoft’s Direct Send feature to form a “highly efficient attack pipeline” in recent
Threat actors are abusing HTTP client tools like Axios in conjunction with Microsoft’s Direct Send feature to form a “highly efficient attack pipeline” in recent

A new Android malware called RatOn evolved from a basic tool capable of conducting Near Field Communication (NFC) attacks to a sophisticated remote access trojan
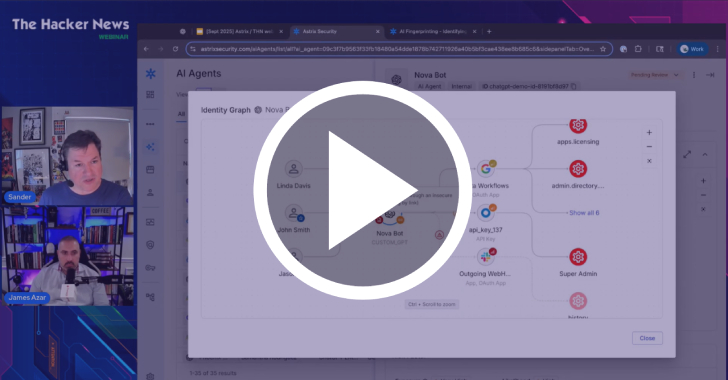
⚠️ One click is all it takes. An engineer spins up an “experimental” AI Agent to test a workflow. A business unit connects to automate
Cybersecurity researchers have disclosed details of a phishing campaign that delivers a stealthy banking malware-turned-remote access trojan called MostereRAT. The phishing attack incorporates a number

Cybersecurity researchers have discovered a variant of a recently disclosed campaign that abuses the TOR network for cryptojacking attacks targeting exposed Docker APIs. Akamai, which
It’s budget season. Once again, security is being questioned, scrutinized, or deprioritized. If you’re a CISO or security leader, you’ve likely found yourself explaining why

Multiple npm packages have been compromised as part of a software supply chain attack after a maintainer’s account was compromised in a phishing attack. The

Threat hunters have discovered a set of previously unreported domains, some going back to May 2020, that are associated with China-linked threat actors Salt Typhoon

Salesloft has revealed that the data breach linked to its Drift application started with the compromise of its GitHub account. Google-owned Mandiant, which began an

Cybersecurity researchers have detailed a new sophisticated malware campaign that leverages paid ads on search engines like Google to deliver malware to unsuspecting users looking
