
Don’t Overlook These 6 Critical Okta Security Configurations
Given Okta’s role as a critical part of identity infrastructure, strengthening Okta security is essential. This article covers six key Okta security settings that provide

Given Okta’s role as a critical part of identity infrastructure, strengthening Okta security is essential. This article covers six key Okta security settings that provide

Threat actors have been observed targeting Internet Information Services (IIS) servers in Asia as part of a search engine optimization (SEO) manipulation campaign designed to

Zimbra has released software updates to address critical security flaws in its Collaboration software that, if successfully exploited, could result in information disclosure under certain

Threat actors have been observed exploiting multiple security flaws in various software products, including Progress Telerik UI for ASP.NET AJAX and Advantive VeraCore, to drop
Cybersecurity researchers have uncovered two malicious machine learning (ML) models on Hugging Face that leveraged an unusual technique of “broken” pickle files to evade detection.
A new audit of DeepSeek’s mobile app for the Apple iOS operating system has found glaring security issues, the foremost being that it sends sensitive

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has warned that a security flaw impacting Trimble Cityworks GIS-centric asset management software has come under active
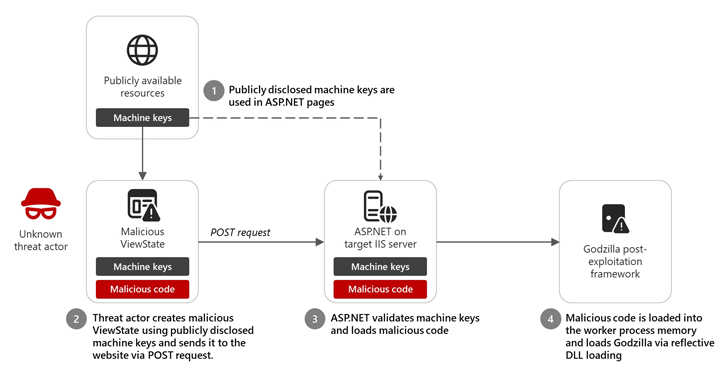
Microsoft is warning of an insecure practice wherein software developers are incorporating publicly disclosed ASP.NET machine keys from publicly accessible resources, thereby putting their applications

The foundations for social engineering attacks – manipulating humans – might not have changed much over the years. It’s the vectors – how these techniques

India’s central bank, the Reserve Bank of India (RBI), said it’s introducing an exclusive “bank.in” internet domain for banks in the country to combat digital
