
5 Reasons Device Management Isn’t Device Trust
The problem is simple: all breaches start with initial access, and initial access comes down to two primary attack vectors – credentials and devices. This

The problem is simple: all breaches start with initial access, and initial access comes down to two primary attack vectors – credentials and devices. This

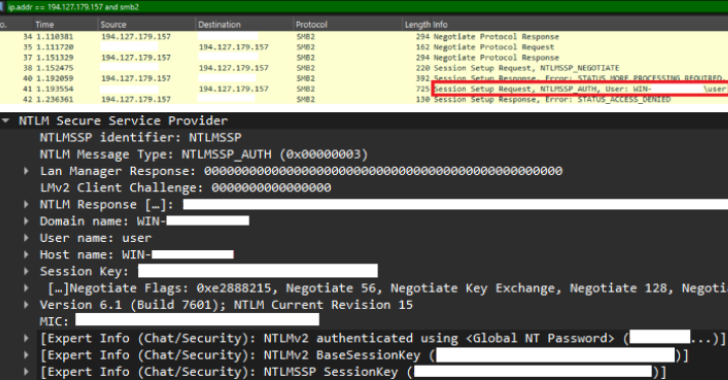
Cybersecurity researchers have disclosed a surge in “mass scanning, credential brute-forcing, and exploitation attempts” originating from IP addresses associated with a Russian bulletproof hosting service

The Russian state-sponsored threat actor known as APT29 has been linked to an advanced phishing campaign that’s targeting diplomatic entities across Europe with a new

Cybersecurity researchers have uncovered three malicious packages in the npm registry that masquerade as a popular Telegram bot library but harbor SSH backdoors and data

ASUS has disclosed a critical security flaw impacting routers with AiCloud enabled that could permit remote attackers to perform unauthorized execution of functions on susceptible

Cybersecurity researchers are warning of a “widespread and ongoing” SMS phishing campaign that’s been targeting toll road users in the United States for financial theft

A new multi-stage attack has been observed delivering malware families like Agent Tesla variants, Remcos RAT, and XLoader. “Attackers increasingly rely on such complex delivery

Your employees didn’t mean to expose sensitive data. They just wanted to move faster. So they used ChatGPT to summarize a deal. Uploaded a spreadsheet
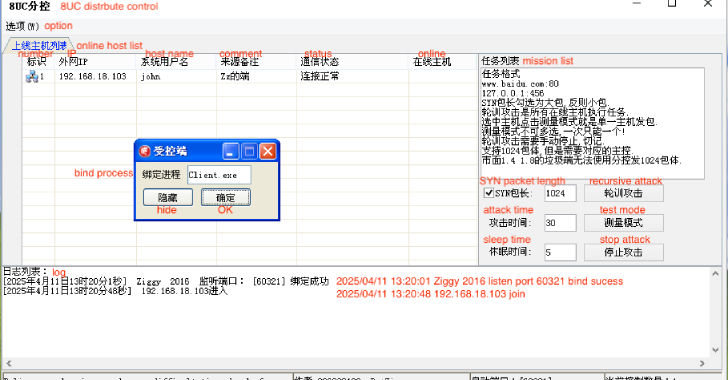
Cybersecurity researchers are warning of continued risks posed by a distributed denial-of-service (DDoS) malware known as XorDDoS, with 71.3 percent of the attacks between November
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added a medium-severity security flaw impacting Microsoft Windows to its Known Exploited Vulnerabilities (KEV) catalog,
