
⚡ Weekly Recap: AI Automation Exploits, Telecom Espionage, Prompt Poaching & More
This week made one thing clear: small oversights can spiral fast. Tools meant to save time and reduce friction turned into easy entry points once

This week made one thing clear: small oversights can spiral fast. Tools meant to save time and reduce friction turned into easy entry points once

A new wave of GoBruteforcer attacks has targeted databases of cryptocurrency and blockchain projects to co-opt them into a botnet that’s capable of brute-forcing user

Cybersecurity researchers have shed light on two service providers that supply online criminal networks with the necessary tools and infrastructure to fuel the pig butchering-as-a-service
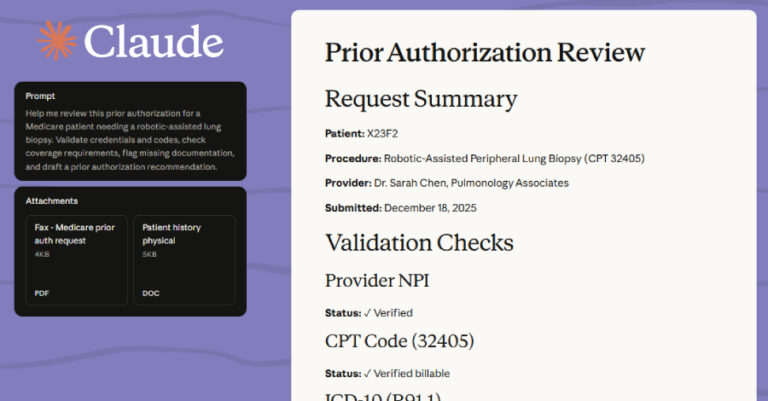
Anthropic has become the latest Artificial intelligence (AI) company to announce a new suite of features that allows users of its Claude platform to better

Europol on Friday announced the arrest of 34 individuals in Spain who are alleged to be part of an international criminal organization called Black Axe.

The Iranian threat actor known as MuddyWater has been attributed to a spear-phishing campaign targeting diplomatic, maritime, financial, and telecom entities in the Middle East

Chinese-speaking threat actors are suspected to have leveraged a compromised SonicWall VPN appliance as an initial access vector to deploy a VMware ESXi exploit that

Russian state-sponsored threat actors have been linked to a fresh set of credential harvesting attacks targeting individuals associated with a Turkish energy and nuclear research

As organizations plan for 2026, cybersecurity predictions are everywhere. Yet many strategies are still shaped by headlines and speculation rather than evidence. The real challenge
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday said it’s retiring 10 emergency directives (Eds) that were issued between 2019 and 2024. The
