
⚡ THN Weekly Recap: Google Secrets Stolen, Windows Hack, New Crypto Scams and More
Welcome to this week’s Cybersecurity News Recap. Discover how cyber attackers are using clever tricks like fake codes and sneaky emails to gain access to

Welcome to this week’s Cybersecurity News Recap. Discover how cyber attackers are using clever tricks like fake codes and sneaky emails to gain access to

Cybersecurity researchers have shed light on a new Golang-based backdoor that uses Telegram as a mechanism for command-and-control (C2) communications. Netskope Threat Labs, which detailed

Google is working on a new security feature for Android that blocks device owners from changing sensitive settings when a phone call is in progress.

Cybersecurity researchers have disclosed a new type of name confusion attack called whoAMI that allows anyone who publishes an Amazon Machine Image (AMI) with a

The North Korean threat actor known as the Lazarus Group has been linked to a previously undocumented JavaScript implant named Marstech1 as part of limited
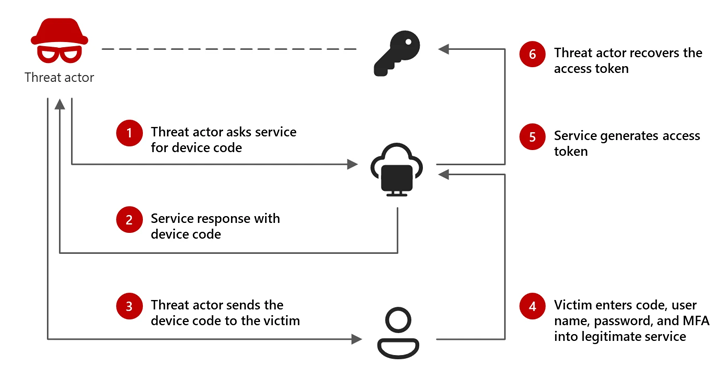
Microsoft is calling attention to an emerging threat cluster it calls Storm-2372 that has been attributed to a new set of cyber attacks aimed at
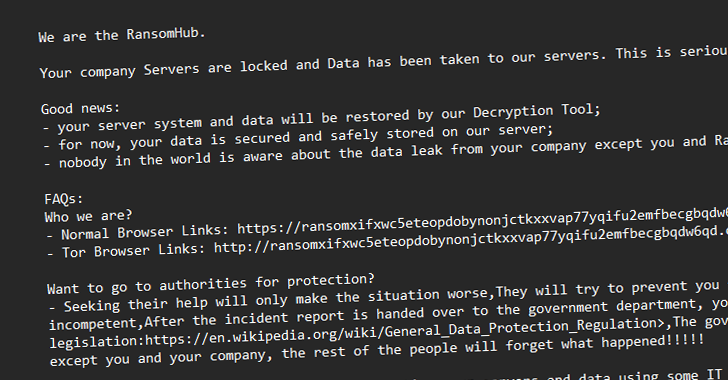
The threat actors behind the RansomHub ransomware-as-a-service (RaaS) scheme have been observed leveraging now-patched security flaws in Microsoft Active Directory and the Netlogon protocol to

Social engineering is advancing fast, at the speed of generative AI. This is offering bad actors multiple new tools and techniques for researching, scoping, and

Threat actors who were behind the exploitation of a zero-day vulnerability in BeyondTrust Privileged Remote Access (PRA) and Remote Support (RS) products in December 2024

A widespread phishing campaign has been observed leveraging bogus PDF documents hosted on the Webflow content delivery network (CDN) with an aim to steal credit
