
Product Walkthrough: A Look Inside Wing Security’s Layered SaaS Identity Defense
Intro: Why hack in when you can log in? SaaS applications are the backbone of modern organizations, powering productivity and operational efficiency. But every new

Intro: Why hack in when you can log in? SaaS applications are the backbone of modern organizations, powering productivity and operational efficiency. But every new

Cheap Android smartphones manufactured by Chinese companies have been observed pre-installed with trojanized apps masquerading as WhatsApp and Telegram that contain cryptocurrency clipper functionality as

The U.S. government funding for non-profit research giant MITRE to operate and maintain its Common Vulnerabilities and Exposures (CVE) program will expire Wednesday, an unprecedented

Cybersecurity researchers have disclosed a malicious package uploaded to the Python Package Index (PyPI) repository that’s designed to reroute trading orders placed on the MEXC
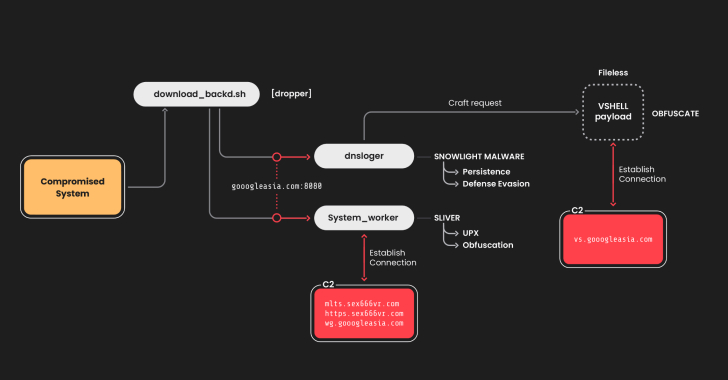
The China-linked threat actor known as UNC5174 has been attributed to a new campaign that leverages a variant of a known malware dubbed SNOWLIGHT and

A critical security vulnerability has been disclosed in the Apache Roller open-source, Java-based blogging server software that could allow malicious actors to retain unauthorized access

Everybody knows browser extensions are embedded into nearly every user’s daily workflow, from spell checkers to GenAI tools. What most IT and security people don’t
The North Korea-linked threat actor assessed to be behind the massive Bybit hack in February 2025 has been linked to a malicious campaign that targets
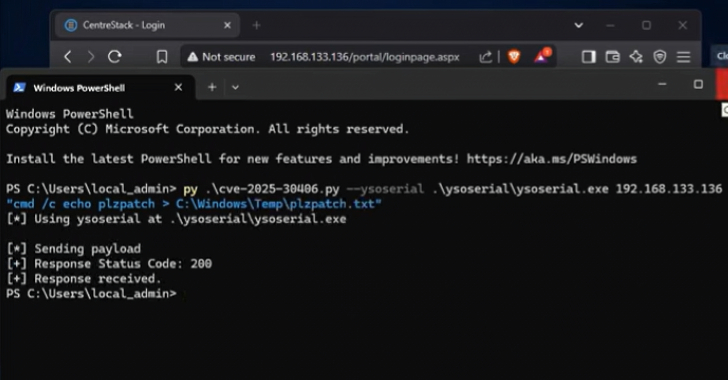
A recently disclosed security flaw in Gladinet CentreStack also impacts its Triofox remote access and collaboration solution, according to Huntress, with seven different organizations compromised
Meta has announced that it will begin to train its artificial intelligence (AI) models using public data shared by adults across its platforms in the
