
CISO’s Guide To Web Privacy Validation And Why It’s Important
Are your web privacy controls protecting your users, or just a box-ticking exercise? This CISO’s guide provides a practical roadmap for continuous web privacy validation

Are your web privacy controls protecting your users, or just a box-ticking exercise? This CISO’s guide provides a practical roadmap for continuous web privacy validation
Cyber threats don’t show up one at a time anymore. They’re layered, planned, and often stay hidden until it’s too late. For cybersecurity teams, the

Cybersecurity researchers have disclosed a malware campaign that uses fake software installers masquerading as popular tools like LetsVPN and QQ Browser to deliver the Winos
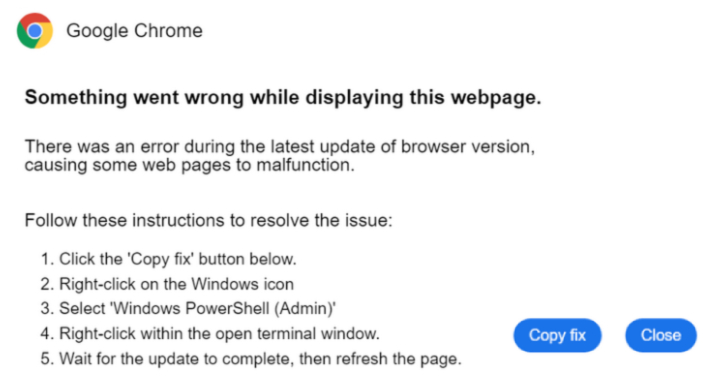
The malware known as Latrodectus has become the latest to embrace the widely-used social engineering technique called ClickFix as a distribution vector. “The ClickFix technique
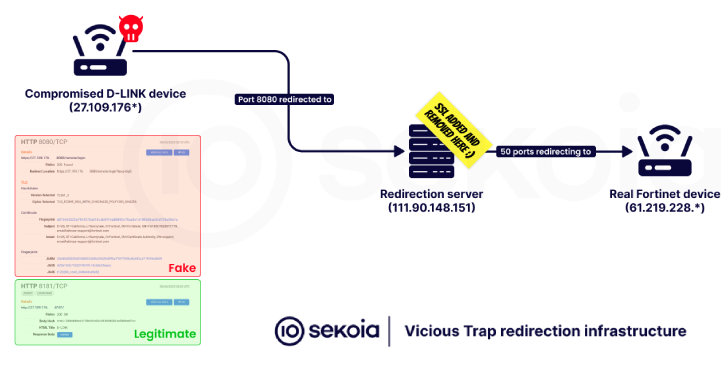
Cybersecurity researchers have disclosed that a threat actor codenamed ViciousTrap has compromised nearly 5,300 unique network edge devices across 84 countries and turned them into

As part of the latest “season” of Operation Endgame, a coalition of law enforcement agencies have taken down about 300 servers worldwide, neutralized 650 domains,
From zero-day exploits to large-scale bot attacks — the demand for a powerful, self-hosted, and user-friendly web application security solution has never been greater. SafeLine
The U.S. Department of Justice (DoJ) on Thursday announced the disruption of the online infrastructure associated with DanaBot (aka DanaTools) and unsealed charges against 16
Cybersecurity researchers have discovered an indirect prompt injection flaw in GitLab’s artificial intelligence (AI) assistant Duo that could have allowed attackers to steal source code

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday revealed that Commvault is monitoring cyber threat activity targeting applications hosted in their Microsoft Azure
