
6 Steps to 24/7 In-House SOC Success
Hackers never sleep, so why should enterprise defenses? Threat actors prefer to target businesses during off-hours. That’s when they can count on fewer security personnel

Hackers never sleep, so why should enterprise defenses? Threat actors prefer to target businesses during off-hours. That’s when they can count on fewer security personnel
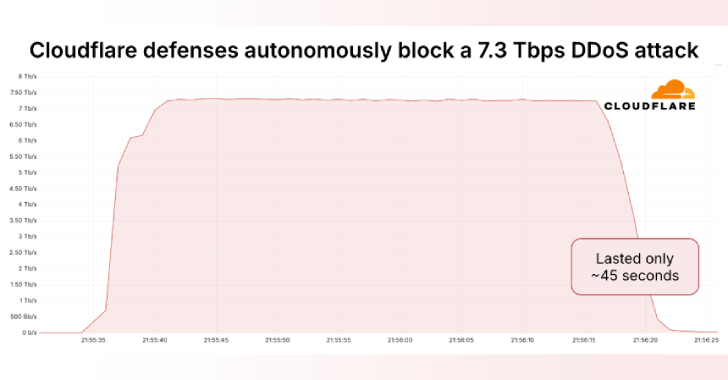
Cloudflare on Thursday said it autonomously blocked the largest ever distributed denial-of-service (DDoS) attack ever recorded, which hit a peak of 7.3 terabits per second

Cybersecurity researchers have uncovered a new campaign in which the threat actors have published more than 67 GitHub repositories that claim to offer Python-based hacking
Cybersecurity researchers have exposed the inner workings of an Android malware called AntiDot that has compromised over 3,775 devices as part of 273 unique campaigns.

DALL-E for coders? That’s the promise behind vibe coding, a term describing the use of natural language to create software. While this ushers in a
The North Korea-aligned threat actor known as BlueNoroff has been observed targeting an employee in the Web3 sector with deceptive Zoom calls featuring deepfaked company

Most cyberattacks today don’t start with loud alarms or broken firewalls. They start quietly—inside tools and websites your business already trusts. It’s called “Living Off
Threat actors with suspected ties to Russia have been observed taking advantage of a Google account feature called application specific passwords (or app passwords) as

Meta Platforms on Wednesday announced that it’s adding support for passkeys, the next-generation password standard, on Facebook. “Passkeys are a new way to verify your

Cybersecurity researchers have uncovered two local privilege escalation (LPE) flaws that could be exploited to gain root privileges on machines running major Linux distributions. The
