
Securing Agentic AI: How to Protect the Invisible Identity Access
AI agents promise to automate everything from financial reconciliations to incident response. Yet every time an AI agent spins up a workflow, it has to

AI agents promise to automate everything from financial reconciliations to incident response. Yet every time an AI agent spins up a workflow, it has to

Cybersecurity researchers have charted the evolution of a widely used remote access trojan called AsyncRAT, which was first released on GitHub in January 2019 and

Governmental organizations in Southeast Asia are the target of a new campaign that aims to collect sensitive information by means of a previously undocumented Windows

The North Korean threat actors linked to the Contagious Interview campaign have been observed publishing another set of 67 malicious packages to the npm registry,

While phishing and ransomware dominate headlines, another critical risk quietly persists across most enterprises: exposed Git repositories leaking sensitive data. A risk that silently creates
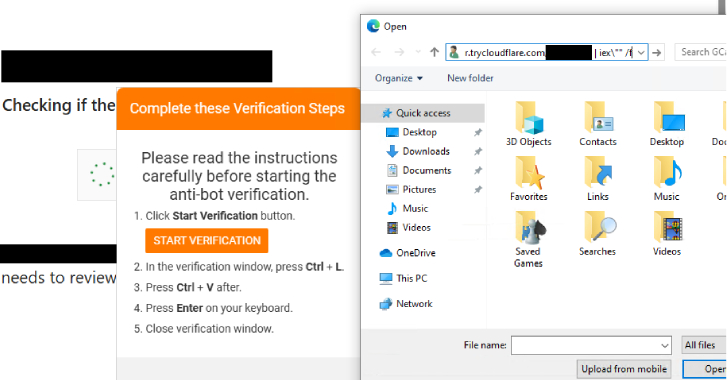
Threat actors behind the Interlock ransomware group have unleashed a new PHP variant of its bespoke remote access trojan (RAT) as part of a widespread

In cybersecurity, precision matters—and there’s little room for error. A small mistake, missed setting, or quiet misconfiguration can quickly lead to much bigger problems. The
India’s Central Bureau of Investigation (CBI) has announced that it has taken steps to dismantle what it said was a transnational cybercrime syndicate that carried
Cybersecurity researchers have discovered a new hacking technique that exploits weaknesses in the eSIM technology used in modern smartphones, exposing users to severe risks. The

NVIDIA is urging customers to enable System-level Error Correction Codes (ECC) as a defense against a variant of a RowHammer attack demonstrated against its graphics
